Securing your information against cyber threats
As the evolution of the digital era continues to make data protection more complicated, Abtran has delivered significant advancements in preventing new and evolving cyber threats.
“It’s always been about the data”, says Abtran IT Security leader Shane O’Callaghan. “From the beginning of written communication and human society, there has been a need to protect information and data. Sure, there’s a lot more data nowadays but safe, accurate, trusted, private data has always been of critical importance.”
O’Callaghan leads the technical side of the information security work at Abtran, Ireland’s largest indigenous BPO. Together with CTO Martin Leahy and the IT and business leadership groups, the team has delivered significant advancements in cyber security over the past few years. Neil Duggan, Abtran internal auditor, takes up the story: “Abtran has always been very conscientious about data integrity. We have been PCI and ISO (9001 and 27001) – accredited for many years and this has meant that our processes and structures have always put data security to the fore. However, over the past few years, due to the expansion of digital online services as well as the changing nature of cybercrime, our focus has had to sharpen in a big way.”
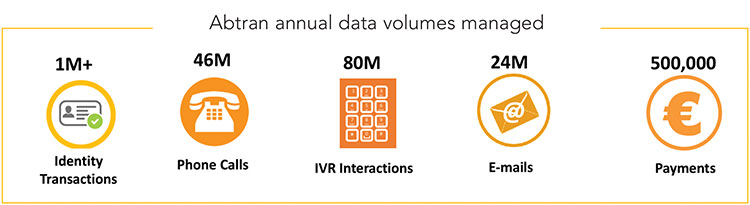
Abtran provides significant levels of contact centre, front-office, back office, digital, mobile and technology-based services across the public and private sectors in both the Irish and European markets. Consequently, the company manages very large volumes of administrative, commercial and personal data. By serving over 1.6 million Irish households the company handles over 45 million telephone calls, 80 million IVR interactions, 25 million-mails and over a million identity management transactions every year. “That’s an awful lot of data” says O’Callaghan, “and we need to have very strict data management and security policies in place.”
Recent developments in cybercrime have completely changed the technical security landscape. With the high-profile attacks as well as accidental leaks and widespread vulnerabilities, it is clear that the very cornerstones of the Internet can be exposed. Recent vulnerabilities like Heartbleed and Cloudbleed show that it’s not just malicious attacks that can cause data loss – it’s just as often caused by internal or systems errors. Long gone are the days when the main threat was a clearly identified virus, worm or Trojan attack – the threat landscape has greatly widened since then to include ransomware, scareware, botnets, internal threats, web app attacks, phishing, data breaches etc.
O’Callaghan continues: “A key feature of the increased sophistication of cybercrime is that the full extent of attacks is no longer visible and frontal. Sometimes it looks like an attack is all about data encryption and the associated ransom demand. However, in almost all cases it’s a copy of your data that they want.” O’Callaghan is referencing a common technique among cybercriminals – create a diversion via a ransom demand and an all-out attack on specific machines or data stores managed by an operation. Such a tactic is extremely effective and draws all the company resources to fighting the attack. Meanwhile a far more dangerous payload has been loaded onto the company’s network as sniffers will have set to work finding key company or customer data with a view to exporting it to an external location. Once the data is exported and illicitly copied there can be a number of impacts:
- the data can be destroyed, modified or corrupted before being surreptitiously reloaded onto the victim’s system at a later date, thereby crippling the victim’s day-to-day business; or
- the data can be sold on to a rival, to a media organisation or generally published.

The highly publicised successes of cybercriminal activities have understandably painted a fairly depressing picture over the past few years. As a result, some organisations have been slow to embrace digital services – and this has meant they have failed to engage with their customers or citizens in a straightforward and easy way. The reluctance to digitise service has led to lost opportunities and the perpetuation of older systems and technologies.
However, many business and service organisations continue to thrive and to embrace digital transformation. Abtran CTO, Martin Leahy, outlines their approach: “Realistically, we had to come out fighting. At Abtran we have always had an easy, secure and straightforward customer or citizen experience as our key goal. Our clients, as well as their customers and citizens accessing public services need to be able to leverage cloud and mobile-based solutions and our challenge was to continue to develop in this direction while at the same time providing an assurance of data integrity. So, we took five basics steps:
- We beefed up our “traditional” information security by deploying powerful anti-malware and discovery applications on every device in the company;
- We carried out a comprehensive and ongoing education of our workforce, alerting them to the signs of suspicious activity and putting fast-track response processes in place;
- We developed our internal technical capabilities by devoting specific roles within the company to cybersecurity management;
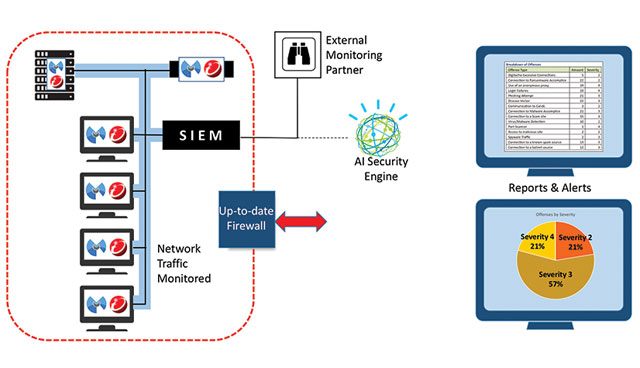
- We invested heavily in SIEM (Security Information and Event Management) technology. This brought us to a level of full monitoring of all network traffic across our business. As well as our own security team we have commissioned a third-party monitoring service so we are monitoring all network traffic 7 X 24 X 365. This also allows us to tap into global AI-driven security engines – we’ve been leveraging IBM Watson since autumn last year and it has been invaluable in predicting, spotting and eliminating threats; and
- We employed rigid discipline around the removal of old plug-ins from our systems – Flash, IE9, ActiveX and so forth. These have well documented vulnerabilities and can only lead to further exposure if retained.
The implementation of the five steps above has worked very well for Abtran – and by extension for all of its clients, customers and data. Cyberattacks and threats are launched every day – every network receives them – often in an innocuous e-mail or cookie. The important thing is to be able to identify suspicious or rogue traffic and to eliminate it.
In addition, as GDPR requirements become mandatory in 2018, the work done on mapping and classifying data as well as the prevention of damage through cyberattacks will ensure GDPR compliance for Abtran – a key requirement in public and private sector services.
Data security has always been necessary. As data theft has become more ambitious and sophisticated, prevention techniques have had to keep ahead of the threat. Companies like Abtran – who manage data from a variety of analogue and digital sources on behalf of public and private sector – have had to be more vigilant than most. However, the results have been impressive, and have allowed the maintenance of an assured data integrity for all of its clients and customers.
Neil Duggan, Internal Audit
Tel: +353 86 858 6754
Email: neilduggan@abtran.com
Kabir Vaderaa, Chief Architect
Tel: +353 86 818 2737
Email: Kabirvaderaa@abtran.com